Norton DNS
Norton DNS is a component of Norton Everywhere, which will eventually give you control over which sites your workers or family members may view, as well as the ability to ban access to sites that are known to transmit harmful information. The user administration panel is still unavailable, despite the fact that OpenDNS beta restricts harmful site access. However, if a cybercriminal person was trying to start a successful malware attack, he or she would have to build a program that would operate successfully, run a number of firewalls, and then convince a user to open a file to run or to get deep into a machine to start the virus. The cyber-thieves soon came to understand that it was simpler to work on the Internet: let the targets come to them.
You might not know, but according to Microsoft itself, application-based vulnerabilities were responsible for more than 90% of all malware assaults in 2008, while operating system software vulnerabilities accounted for only 6% of all malware attacks. Criminals have easier access to target computers thanks to applications like Web browsers, instant messaging programs, and e-mail systems. Using a Web browser to lead a victim onto an infected site is one way cybercriminals can expose their computer to an attack. This Web site could be legitimate, or it could be phishing, which is when a site is designed to look almost identical to that of a legitimate, trustworthy company.
Understanding Norton DNS
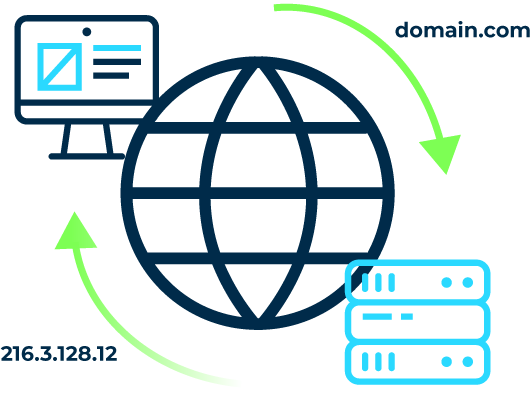
The Domain Name System (DNS) is the Internet’s phonebook. Domain names, such as nytimes.com or espn.com, are used by humans to access content online. Web browsers communicate via Internet Protocol (IP) addresses. DNS converts domain names to IP addresses so that browsers may access Internet resources.
Each Internet-connected device has a unique IP address that other machines may use to locate the device. DNS servers reduce the requirement for humans to remember IP addresses like 192.168.1.1 (in IPv4) or more complicated modern alphanumeric IP addresses like 2400:cb00:2048:1::c629:d7a2 (in IPv6).

Working of DNS Explained
DNS resolution is the method or process of converting a hostname (for example www.example.com) into a computer-friendly IP address (like 192.168.1.1). Each device on the Internet is assigned an IP address, and that address is required to locate the proper Internet device, much as a street address is used to locate a certain residence. When a user requests a webpage, a translation must take place between what the user puts into their web browser (example.com) and the machine-friendly address required to access the example.com webpage.
Norton DNS - Understanding the Anatomy
Norton DNS is a service that enables quicker and more reliable online browsing while still providing basic protection. It does not necessitate the use of a client. You may use Norton DNS on individual PCs or enable Norton DNS on your router to secure all of your home’s devices.
Norton was among the first free public DNS providers to give some level of security. They had three policies:
A — Security (virus, phishing sites, and scam sites): 199.85.126.10
B — Security + Pornography: 199.85.126.20
C — Security + Pornography + Other: 199.85.126.30
Users may use this to build a DNS-based firewall, blocking access to undesirable material. Symantec has been researching malware attack behavior and how it spreads. Norton Secure DNS is also said to be a member of the Anti-Phishing Working Group. An industry organization devoted to educating consumers about and eliminating Internet fraud.
Norton Safe DNS has since been launched as a free service for all non-commercial uses. All a person needs to do from the Norton DNS Server site is to take a few easy steps to convert their computer over to the Norton Connectsafe DNS system. There’s even a verification website that can tell a user whether they’ve set it up correctly.
How can it Help?
Norton DNS, like any other DNS service. It will transform the text-based Web address into the numerical IP address and redirect the user to the desired Web site. Norton DNS, on the other hand, not only accomplishes that, but it also rapidly runs a check through Norton’s Safe Web database to ensure the site isn’t known for any issues, such as phishing or malware assaults. In addition, a person may go to safeweb.norton.com to discover if any Web URL is in the database without actually visiting it. Furthermore, if there is a red signal, Norton DNS will show extensive details on why Symantec feels the site is malicious.
Despite the fact that it performs more services than a standard DNS, many people believe that the Norton DNS runs quicker. It also has 17 hosted data centers across the world to provide quick service. Given the fact that it is free, Norton DNS is not meant to be a replacement for a comprehensive solution to antivirus, antispam, and other types of anti-intrusion-based malware. Norton DNS, on the other hand, offers an extra layer of security to fight hazardous Web sites, the current way hackers use to assault their targets.
How to Set Up Norton DNS?
To begin with Norton setup, follow the steps given below.
- From the Start Menu, select Control Panel.
- View network status and tasks by clicking the View network status and tasks button.
- Select the network connection to which you wish to switch to Norton DNS.
- Select Internet Protocol Version 4 from the drop-down menu.
- Click on Properties once again, and then enter the Norton DNS IP addresses provided below.
- At a command prompt, type ipconfig /renew to refresh your IP setup.
- Verify the change by running ipconfig /all at a command line and ensuring that the DNS servers display the updated values.
Steps for DNS Lookup
In most cases, DNS is concerned with translating a domain name into the proper IP address. To understand how this process works. Trace the course of a DNS lookup from a web browser to the DNS lookup process and back again. Let’s go over the steps one by one.
- When a user enters ‘example.com’ into a web browser, the query is routed across the Internet and received by a DNS recursive resolver.
- After that, the resolver requests a DNS root nameserver (.).
- The root server then responds to the resolver by providing the address of a Top Level Domain (TLD) DNS server (such as.com or.net), which holds information for its domains. When we search for example.com, we are sent to the.com TLD.
- After that, a request is sent by the resolver to the .com TLD.
- Following that, the TLD server answers with the IP address of the domain’s nameserver, example.com.
- Finally, the recursive resolver queries the domain’s nameserver.
- The nameserver then returns the IP address for example.com to the resolver.
- The DNS resolver then returns to the web browser the IP address of the domain that was originally requested.
4 Types of DNS Servers
DNS Recursor
A DNS recursor is a server that accepts requests from client machines via programs such as web browsers. The recursor is then often in charge of making extra queries in order to satisfy the client’s DNS query.
Root Name Server
The root nameserver is the initial stage in converting (resolving) human-readable hostnames into IP addresses. It may be compared to an index in a library that links to various book racks – generally. It acts as a reference to other more particular locations.
TLD Name Server
Think of a top-level domain server (TLD) as a specific rack of books in a library. This nameserver is the following stage in the search for a certain IP address. It hosts the last element of a hostname (the TLD server in example.com is “com”).
Authoritative Name Server
Think of this ultimate nameserver as a dictionary on a book rack. Where a specific name may be translated into its definition. The last stop in the nameserver query is the authoritative nameserver. If the authoritative name server has access to the requested record. It will return to the DNS Recursor that made the initial request for the IP address for the requested hostname.