Today’s era is running around the internet that evolves everything bad and good in it. The Internet gave us so many productive things and also for entertainment. We spent hours surfing the internet without thinking twice that the internet could be a dangerous place to put up so much data related to you. These data could be personal and professional too. There are people who would be lurking for you to make some mistakes and they take advantage of your information for their own good. Heartbleed is one such bug that is used to intrude on your online data by many cybercriminals.
This post is all about Heartbleed and how we can get rid of this bug from your system.
What is Heartbleed?
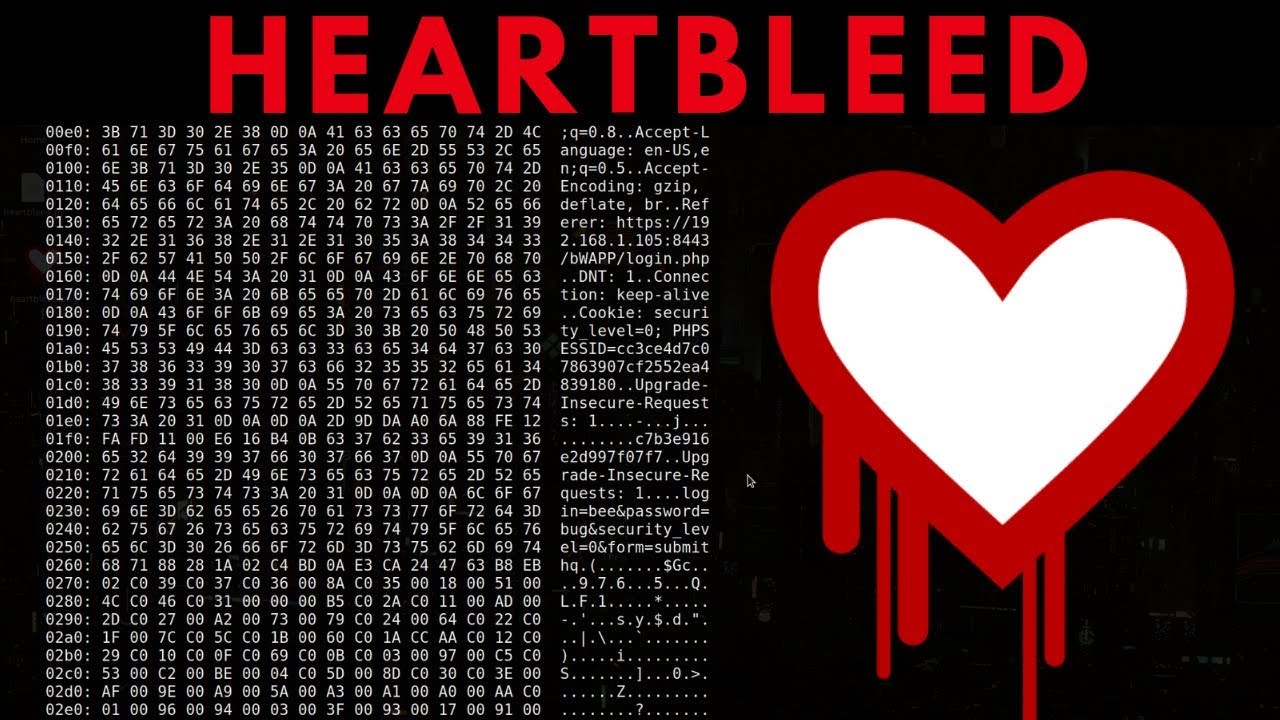
Heartbleed is a bug that attacks the vulnerability in open-source code that was first discovered in April 2014 by Computer security Researchers. When an open SSL (Secure Socket Layer) has some flaws, the Heartbleed bug takes place in it and allows the attackers to access sensitive information. In short, anyone with an internet connection on their system can use this bug to access any vulnerable system to read their memory, and this bug leaves no evidence of compromisation behind it.
OpenSSL is the most popular open-source cryptographic library that provides the user’s Secure Socket Layer (SSL) and Transport Layer Security (TLS). A user can implement these two open-source on his/her website to encrypt the traffic on the internet. The heartbleed bug gets implemented in the OpenSSL cryptographic library. That is why it is also called an implementation bug. Even though the bug is implemented in the OpenSSL library, it’s nothing to do with the SSL and TLS protocol. The vulnerability affects the OpenSSL code that handles heartbeat extensions for SSL and DTLS.
Also Read: Norton Utilities Premium
How does Heartbleed work?
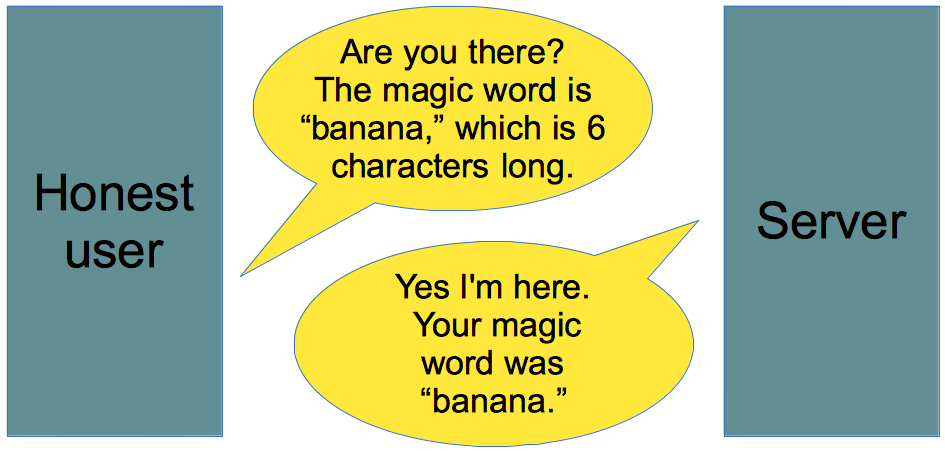
With the help of TLS/SSL protocol is the bridge between two computers to communicate, that is called the heartbeat. When there’s improper input validation in the OpenSSL installation of the TLS heartbeat Extension the Heartbleed bug gets its start from here. Let me explain the work in a detailed manner.
When two computers start communicating with each other and they know that they are connected even when the user isn’t working on the computer such as downloading or updating. The connection gets established when one computer sends an encrypted message to another computer called heartbeat. Now the second computer replies back with an encrypted message to confirm that the connection between both computers is safe. Occasionally, hackers send cleverly formed malicious heartbeat messages from one to another computer and the receiver gets tricked and it replies to the malicious heartbeat message and allows the hacker to enter into its data. Specifically, a vulnerable system can become the victim of this transmitting bug called a heartbleed attack.
What are the Impacts of these Bug Attack Leaves?
There are numerous impacts of heartbleed attacks on any system and any internet user can avail it.
- If the system is bugged with heartbleed anyone on the internet can hear the memory of the bugged system
- There is a lot of sensitive data on the internet that can be extracted such as session identifier, username, passwords, token, and sometimes server’s private encrypted keys.
- This bug leaves no such evidence of its appearance on the system
- Through accessing the heartbleed an attacker can read 64 kilobytes of server memory
What is The Heartbleed Code?
As we are aware a heartbleed attack is caused due to some malicious code or mistake in coding. These mistakes in coding are
memcpy(bp, pl, payload);
memcpy ( ) is a command prompt that copies data.
bp is the place where the data get to save after copying
Pl is where the copied data came from
payload is the length of the data that get copied
The bug enters the system with only one mistake: that the users never check if the amount of the data in pl is equal to the value given of payload.
The most important thing in this bugging is that OpenSSL is open-source software. The code is visible to everyone but nobody notices the elementary coding error.
How To Avoid these Attacks?
Patches were unrolled for OpenSSL directly when the vulnerability was announced, and altogether likelihood, most formerly vulnerable servers are updated by now, but it can’t hurt to check if you are not sure — it is often possible that some server that’s important to you has been chugging along for years without a correct upgrade. Pentest-tools.com features a free web-based test that allows you to input a URL to see if a server has been properly patched.
The thanks to fixing the Heartbleed vulnerability is to upgrade to the newest version of OpenSSL. you’ll find links to all or any of the newest code on the OpenSSL website.
If you’re interested in the code that implements the fix, you’ll check out it — in any case, OpenSSL is open source:
Note: You are required to first read type and payload length
if (1 + 2 + 16 > s->s3->relent) return 0; /* silently discard */ hbtype = *p++; n2s(p, payload); if (1 + 2 + payload + 16 > s->s3->rrec.length) return 0; /* silently discard per RFC 6520 sec. 4 */ pl = p;
The first part of this code makes sure that the heartbeat request isn’t 0 KB, which may cause problems. The second part makes sure the request is really as long because it says it’s.
If you discover that a server under your control has been left vulnerable a few times, there’s more to try than simply updating the OpenSSL code. As an example, you ought to change the SSL certificates employed by the servers, since they’ll be compromised without leaving a trace. It is important for all internet users, specifically those who have an account on the internet, to frequently change their passwords.
Check out: How to get strong password protection?
Conclusion!
Regarding all the above information related to a bug Heartbleed will assist you to understand the bug closely. This post will tell you how this bug works and how to avoid heartbleed attacks from your system. If you like this article please comment down below. And also do not forget to read other articles on our website.
Author Profile
Latest entries
Technology2023.04.20How To Connect Roku To TV? Easy Guide To Follow
Technology2023.04.20How to Connect Nintendo Switch to TV? (With and Without Dock)
Technology2023.04.205 Best Barndominium Design Software (DIY & Professional)
Technology2023.04.20What Is The Relation Between Behavior-Driven Development And Agile Methodology?