Well, in the digital world, we often get several kinds of malware attacks that will bring insecurity to our data and personal information. In order to save you from any such hindrance, we are here to provide you a detailed guide on ransomware removal. This guide will surely provide you with better help till you go towards the ending part. We will cover every possible thing related to the topic. So, you don’t need to go here and there to get answers as the post has everything in its pocket.
But, we would like to inform you that we will not directly jump to the removal of ransomware. Instead, we will first give you a basic understanding of the definition, how it enters the system, what are the types, and then jump to the solution. So, it would be a request to read the full post because a little knowledge is a dangerous thing. And, we do not want to put you in any kind of danger with less awareness of the topic. So, this is our basic concern to help you in every possible way. Now, let’s learn what the definition of ransomware is.
Ransomware: An Introductory Definition
Ransomware appears in the disguised malicious software that locks and encrypts all the relevant data from the device. Not only this, but it also asks for a ransom to bring the data back to that particular device.
This is a great way for cybercriminals to extort money from these kinds of victims. The general way of ransomware’s entrance is through the ruining of the security hole. Much vulnerable software becomes corrupted because of these techniques. Due to its demands for recovery, the software is named ‘Ransomware.’ The PC framework stays corrupted and harmed until the victims fulfill the ransom amount.
The issue of ransomware is a big one. Everyone needs to be more attentive and focused on these kinds of malware because they can prove a big threat to you. It can appear in the shape of a virus scanner to hide its real intention with you. Many victims have experienced it as a scary dream with all those threats and ransom that to be made through credit cards, and cryptocurrency. Whether it is a business, an individual, a company, an organization, or anyone can become the victim of this malware.
You might come across the term Ransomware-as-a-Service or Raas which means the services to other cybercriminals provided by some ransomware authors. Well, there are a lot of unknown facts related to this ransomware virus. Keeps on learning their different variants and how they enter into your system and how you can fight against them by following this entire guide.
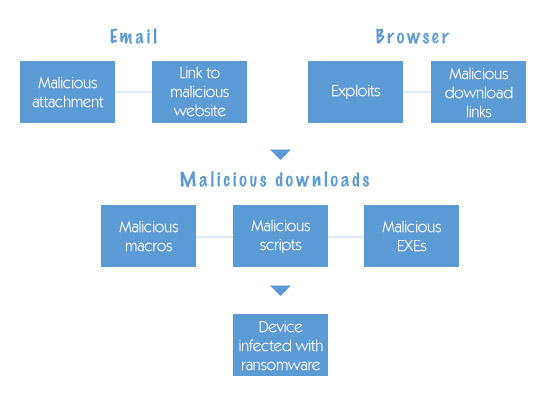
How does Ransomware Enter into the system?
Ransomware can enter into the system in many different ways. It can corrupt your system with several kinds of infections. Malicious spam or mailspam is on the top of the common ways for making its entrances. The procedure contains some unsolicited emails having links to make the user enter into the malicious websites.
Cybercriminals trick people to click open attachments of links via social engineering. Earlier the links appear to be legitimate but secretly they carry some malicious program going to hit our computer framework. The most known example of these kinds of ransomware is the posing of cybercriminals as the FBI. Through this, they scare some users and make them pay a huge amount of ransom for the sake of unlocking their files.
Malvertising is yet another infectious way used by many cybercriminals. It is one kind of malicious advertising that’s where it takes its name. It is one of the great ways to spread malware in the form of advertisements. Sometimes, the user gets into the corrupting world without tapping on an ad. All of the victims’ information and essential details stored in the computer are delivered to those cybercriminals.
Well, there can be an invisible web page element and an infected frame that becomes the bridge between the victim’s device and the ransomware. Iframe brings it directly to an exploit landing page while exploit kit is used to provide attacks from the landing page. It is also termed a drive-by-download because of the user’s unawareness of these kinds of attacks.
So, these are the two ways through which ransomware can enter into the system. Now, you want to know what other kinds of ransomware are. If we speak our mind then move on to the next section containing various kinds of ransomware that can disturb the territory that you feel through your system.
Various Kinds of Malicious Ransomware
Well, there are mainly three kinds of ransomware that are going to be described from mild to dangerous. You can consider the list below to know everyone.
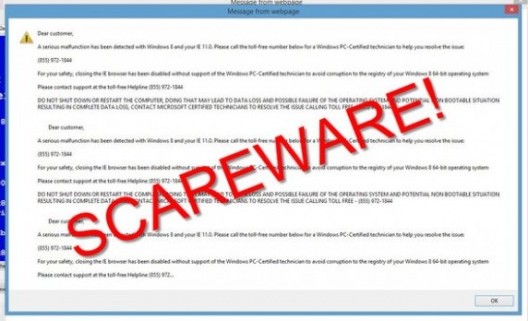
Scareware
Most people consider scareware as scary but it is not like that. It has scams like tech support and rogue security software. There comes a message with the claim that there is a presence of malware and the user of the system needs to fulfill the demands as a ransom to eradicate the pop-up message. Although the pop-ups appear continuously when you execute nothing as written all your files remain safe and secure.
You can consider the help of a cybersecurity software program like Norton ransomware removal to have full security of your device. You don’t need to be bothered by any kind of malicious and infectious program as Norton will provide all the tools to aid you in this. Due to these variants in ransomware, we have seen a lot of emergences in security software too.
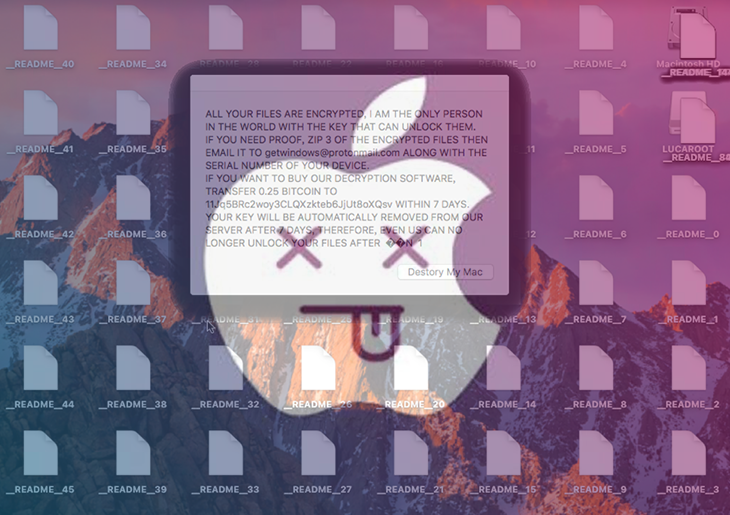
Encrypting Ransomware
With the name, we can get the idea that encrypting ransomware grab the files stored in your system and then encrypt them. Not only this but it also asks for payment in the form of ransom to redeliver the files to their real owners. The idea behind them being so threatful is that no one can secure and restore the files once the cybercriminals snatched them up. Money is the only way to get back full access to your data.
Screen Lockers
If ransomware like screen lockers get into your system then it becomes rare to get your PC back. Whenever the user tries to start the system, a window will pop up stating that illegal activity has been detected. You can see an image of the US Department of Justice seal with the note of paying a fine. It should be noted that the real FBI does not favor any of these kinds of activity unless they suspect you of cybercrimes, piracy, and child pornography.
Raas
Ransomware as a Service or Raas is another kind of malicious program. The program enables cybercriminals to do anything with PCs having your information. Not only do they demand ransom but also manage decryptors to bring back the data access.
Doxware
The malware initially threatens to disclose all of your data if you neglect the ransom amount. We have seen many instances of these kinds of malware that seek money from people who tend to save their personal and sensitive photos on their devices. Most people get trapped and, to, get back their information, they become ready to provide the ransom.
Crypto Malware
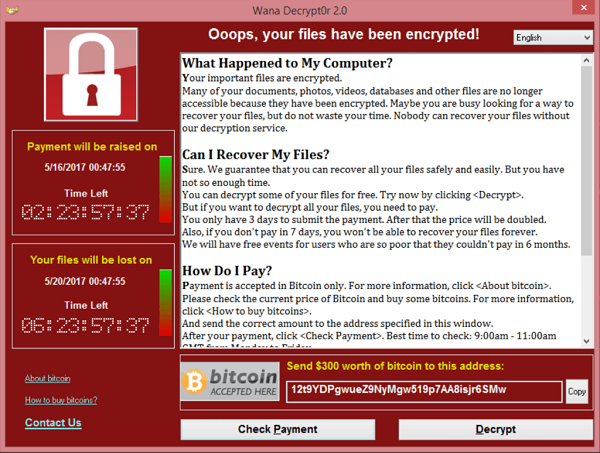
Crypto Malware provides some threatful damages to your folders, hard drives, and files. You might hear of the destructive 2017 WannaCry ransomware attack that proved threatful to thousands of Windows Operating systems. Every victim is demanded to provide money in the form of Bitcoin if they want to restore the data.
Mac Ransomware
In 2016, Mac has threatened by the first-ever ransomware KeRanger. This program takes the help of a malicious app named Transmission to encrypt the files of its victims. Just like mac ransomware, mobile ransomware also uses an app that notifies the user about the illegal activity becoming the reason for shutting down of mobile.
Some of the Historical Evidence of Ransomware Attacks
Although ransomware was introduced to target individuals, later on, they move the focus towards some big enterprises to demand the bigger amount. Check out the full section to know how it brought, evolved and what its position in todays’ timeline.
PC Cyborg
PC cyborg appears in the late 1980s. The carrier of this malicious program is AIDS researcher Joseph Popp. He used around 2,000 floppy disks to conduct his operation. These disks consisted of malicious devices that can get all the data from C: directory files. If the victims completed around 90 reboots in their systems then they would probably get into the trap.
GpCode
GpCode is developed in 2004. This is a weak form of RSA encryption that can attack the personal files of several users around the world.
WinLock
WinLock brings danger to the victims by displaying some pornographic elements on their system screen. The victims become unable to do anything because they are locked by this malicious program. The only way to get rid of it is by paying a ransom. It generally makes its entrance in 2007.
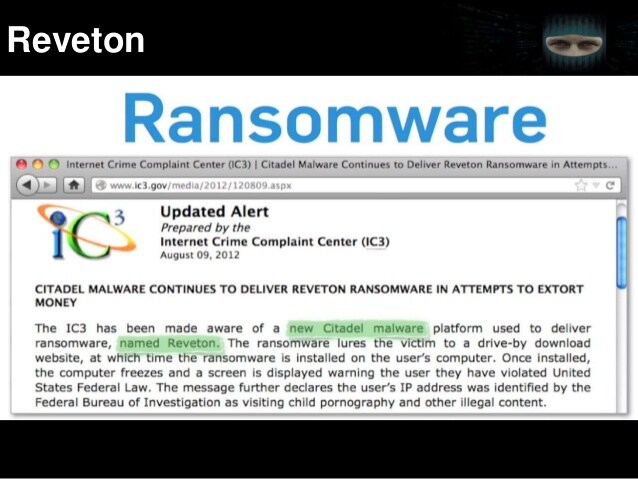
Reveton
As we mentioned above, it displays the image of FBP or an enforcement agency to trap the victim in the false allegations of committing crimes. Many victims complete their ransom wish by providing them with a fine. Rather than this CryptoLocker and Locky are other ransomware that emerged in 2013 and 2016. As we have told you about them in a descriptive manner so we don’t want to consume your time in learning the same thing again and again. So, now moving into the next evidence of ransomware.
WannaCry
It appears to disturb businesses all over the world. In 2017, WannaCry attacked many businesses and demanded ransom to retrieve their essential files and data.
Sadinokibi
It is developed in 2019 by a cybercriminal who preferred Managed Service Providers abbreviated as MSPs such as dental offices.
Darkside
Darkside is created in 2021 that takes help from Ransomware-as-a-Service (Raas) model to kneel the bigger corporations such as Colonial Pipeline. Many cybersecurity officials claim that Russian hackers are the men behind its creation.
Revil and Sodinokibi
These two are also developed in 2021. Cryptocurrency is the ransom amount that they demand unlocking the files. You may hear of the biggest meatpacker in the world, JBS gets into the trap of cybercriminals.
Get to know the Targets of Ransomware
Well, there is no specific target for ransomware attacks but we can take some idea from its name that it decides its targets at the thought of yielding some amount. The bigger the organization is, the more ransom it is provided. So, the ability to target users are depending on the size of the organization. We have provided here the four organizations or groups that may appear on the target list of those cybercriminals.
-
Groups with less security
Every cybercriminal wants to attack those groups or organizations that consist of lots of money with less security. For instance, universities share files in a huge amount but lack security concerns so cybercriminals may target them for their desired ransom.
-
Organizations that can pay instantly
There can be some organizations in the list of these hackers that can provide for ransom instantly. Several groups like banks, government agencies, medical facilities, and lots more can appear on the list. Attack on Colonial Pipeline is the recent instance that has made the payment of around 4.4 million in Bitcoin.
-
Corporations with Sensitive data
There are lots of corporations among us that consist of sensitive data like banking and law firms. So, targeted on them can bring lots of benefits to these cybercriminals. Not only do these corporations occupy money but also the data that can bring anyone into danger.
-
Bigger Enterprises in the Western Side
We are all aware of how the western side is evolving in terms of money and other things. The bigger the world is the better it provides the opportunity to cyber criminals to make an instant attack on these corporate worlds.
Techniques to Never Encounter with Ransomware
Many of the readers may read this post to get this answer. Well, we will directly start with it but there would be no use of it if you don’t come across the real threat that it can provide to your data. Now that you have understood every essential point about ransomware, it’s time to learn some of the most efficient techniques to fight back to them. You will be provided with all the skillful techniques so keep on scrolling down.
-
Make sure to restore your data
It would not secure your data from getting stolen but it saves your money from getting wasted in the name of ransom. Moreover, you can still get through all your data even after cybercriminals stole it.
-
Download and Install Norton 360 ransomware removal tool
Norton 360 is one of the best tools on the list of antivirus software. It has several users worldwide. Features like anti-theft identity, parental control, a quick scan, and many more make it into unique reliable antivirus software.
-
Stay Up-to-date
Everyone needs to make regular updates to their programs, security software, and operating system. With the update, the program uses the latest security patches to fight back that ransomware
-
Stay Focussed when Online
There comes several malicious websites whenever you come online. With your one click, you can welcome your threats so make yourself aware while surfing anything online.
-
Avoid Email Attachments
We often get various emails and messages containing some links and attachments. You need to avoid all of these because some malware can secretly hide on them.
-
Avoid the use of public Wi-Fi
Public Wi-Fi can prove to be very risky for your data. Cybercriminals can fetch your information from that so try to use VPN (Virtual Private Network). You must need to know that Norton VPN is also available for various users. If you want to safeguard your information then don’t forget to use it on your device.
Pointers that help to Fight against Ransomware
If somehow ransomware emerges into the system even after considering the above techniques then use these pointers given below. This will surely help you in many ways to fight against ransomware.
- First of all, use any of the security software. We would recommend you to check out the Norton products as it is fully based on antivirus software. You can find here many options according to your devices and requirements like Norton Mobile Security, Norton 360 variants, and Norton Secure VPN. With this software, you can easily detect and protect your program from corruption bring into by malicious activity.
- You must try to update your Operating system on a weakly basis or whenever the new update appears. As many updates consist of new security patches that help in tackling the issue.
- Always create a backup of your essential data to an external hard drive or a place that is safer than your system. Cybercriminals lose their power if they get to know that you have a copy of that. Also, you need to locate all your backups offline because hackers can again get back to them if you place them online.
- You need to be strong here as we are going to tell you that don’t ever pay the amount demanded by these hackers. Many hackers think of it as a source of generating money and they continue to do so without fulfilling the promises of giving your money back to you.
- Don’t forget the cloud services that help in retaining previous versions of files along with all the encrypted data.
How to remove Ransomware from the device
Well, this is a frequently asked question from many victims of ransomware. So, we have tried to provide you the answer. In order to remove ransomware, we have to do certain things on our device that will be discussed below. So, if your data is also in threat then learn these pointers.
- You can remove the malware just by resetting the system to its factory settings. For this, you need to first back up your data externally or in the cloud.
- As ransomware spread from internet connections so we try to remove all internet connections.
- Always use a decryption tool to get back your data.
- We would also suggest you use security software like Norton but if you are a victim of screen-locking then it might not provide you the help that you desire.
- Restore the backup placed in the external location.
If you conduct any of the operations after malicious ransomware corrupts your system then surely you will rescue yourself from getting into a trap. If you read this post for future awareness then make sure to use the Norton software. With the power of each software, you can easily eliminate any of the malicious activities preparing to take shape into your device.
Final Word!
As the topic said, we have provided you with almost every relevant section. From the starting of ransomware to the key points to remove it, here you will resolve all your query. Although it is one of the worst malware, with the pointers you can get rid of it easily. Always keep in mind to prepare a backup of your data to deprive the hackers of an opportunity to spy on our system.
Also, neglect the ransom amount because with the following methods you can get back to your data without providing them a single penny. In this difficult situation, you need to become more focused on all the substitute ways to help you out. If you want to know more about these kinds of viruses and the techniques to troubleshoot them then bookmark our site as we have covered topics like the Trojan Virus and many others.
Author Profile
Latest entries
Technology2023.04.20How To Connect Roku To TV? Easy Guide To Follow
Technology2023.04.20How to Connect Nintendo Switch to TV? (With and Without Dock)
Technology2023.04.205 Best Barndominium Design Software (DIY & Professional)
Technology2023.04.20What Is The Relation Between Behavior-Driven Development And Agile Methodology?