VPN services to your devices are far better than keeping them in terrible situations. In these critical technological conditions, you must understand the requirement for a protective shield for your connections. The installation process of a VPN is much easier than other crucial points of the network. Express Vpn apple tv is among the devices on the wall of data stealing and privacy concerns issues. You are free to choose your plan as per your requirements. The company has many offers to stabilize the privacy of tech products.
With all the simple formulas, we are here to guide your device connected to the internet.
What is Express VPN Apple TV?
To stabilize your privacy concern in internet connection with apple tv, you need to have a shield as an express VPN. It makes your network risk-free and secure. Although the benefits of the express are enough in number, we should remember that it is for our safety and privacy. This criterion will hold you to buy this product and allow you to breathe free while engaging with the devices.
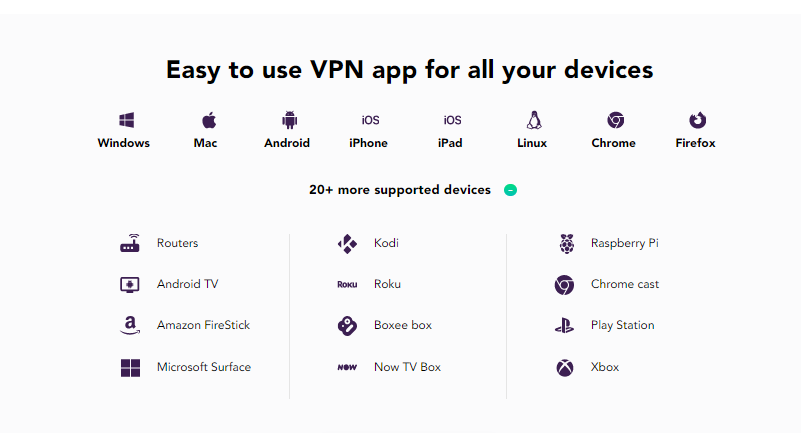
On that note, we should not forget the next thing to notice is you can directly connect this expressvpn apple tv to the router. That is how you will enjoy one service on all your other devices. Furthermore, there is no need to make efforts to change the locations as it allows you a single click option from the remote control.
One extra feature you will get with this is a media streamer to enhance your experience with your location’s existence. You may have the benefits of this VPN express apple tv in the world. Meanwhile, make sure to not forget about the generations of the apple tv this VPN Supports. All in all, this is a super easy plan to save your home network.
Apple TV Generations
You may know the generations of Apple tv. It is the case with every product of the apple company. The global market company TV has been out for many generations. You must be aware of the names of the generations.
The first generation, second generation, third generation, fourth generation, and lastly, 4k are out to connect with express VPN services. The thing is, you must know the process of downloading and installing this VPN to cover your security.
How to Set Up your Express VPN Apple TV?
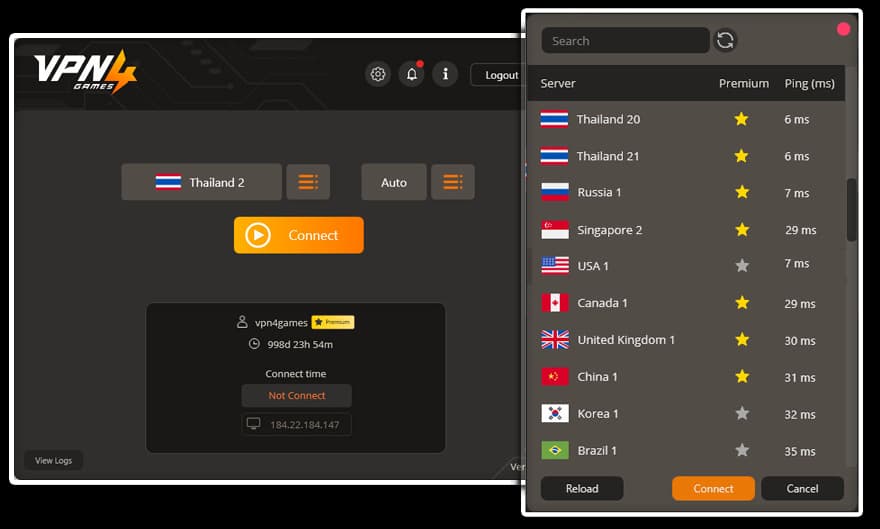
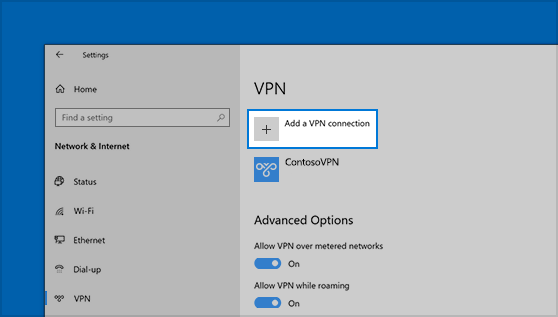
This paragraph will cover your learning for setting up your apple tv with an Express VPN. DNS setting is an option to connect your VPN with devices not following direct VPN services. This DNS setting will coordinate with the setting given by the company as a media streamer to maximize your security within the device or the internet connection. To make a setup step ahead follow the required guidance.
1. MediaStreamer with DNS Setting
Apple tv express VPN will help you streamline your geo-restricted content. First, go through the official website to sign in to your account. The prime component is your IP Address here. You should have a DNS IP address by signing into the express page to set up the procedure. Be careful to change the settings of your Television.
Go to the open setting option by clicking on the network, and choose your internet connection. Here you have to make changes according to your network. No matter what, you have Wifi, Ethernet, or direct wire connection changed according to the condition.
In the last step, proceed to the DNS manual setting and add the media streamer IP address you got while entering into the page setup of ExpressVpn. Restart your device and enjoy the network.
2. Router connection
In our summary paragraph, we have told you the best way to express a VPN setup. We will give you details of that procedure. The router connection benefits are numerous, and you choose this according to your connection. Go to the play store to download the application and complete the process manually. Furthermore, complete the installation and go to the setting option of your apple tv to choose the wireless configuration option to combine all your devices with one router.
3. Use AirPlay to Stream on Apple TV
With AirPlay, you can stream videos from your iPad, Mac, or iPhone and cast them on APPLE TV as well. Run an ExpressVPN app on your mobile device or system to unlock the content and stream it. If you use tvOS 14, you have the option to stream in 4K too. With ExpressVPN, you not only can unblock restricted video content but also get complete security protection from a VPN.
You can unblock Netflix on Airplay by running ExpressVPN on your router. Let’s check out the detailed steps:
Follow these steps to use ExpressVPN with AirPlay on Apple TV:
- Firstly, download the app
- For Mac users – Open ExpressVPN app. Click on > Preferences > General. Tick the option “Allow access to devices on local network”. Or else, Mac won’t be able to discover the Apple TV.
- Next, connect to a VPN server.
- Open the streaming service and watch your favorite content.
- To enable AirPlay video streaming on your smartphone, clicking on the AirPlay icon (you will find in on video window). If you are a Mac user, tap on the AirPlay icon first and then on Apple TV. Make sure Apple TV and your mobile device are on the same Wi-Fi network. Finally, you can see your content on your TV.
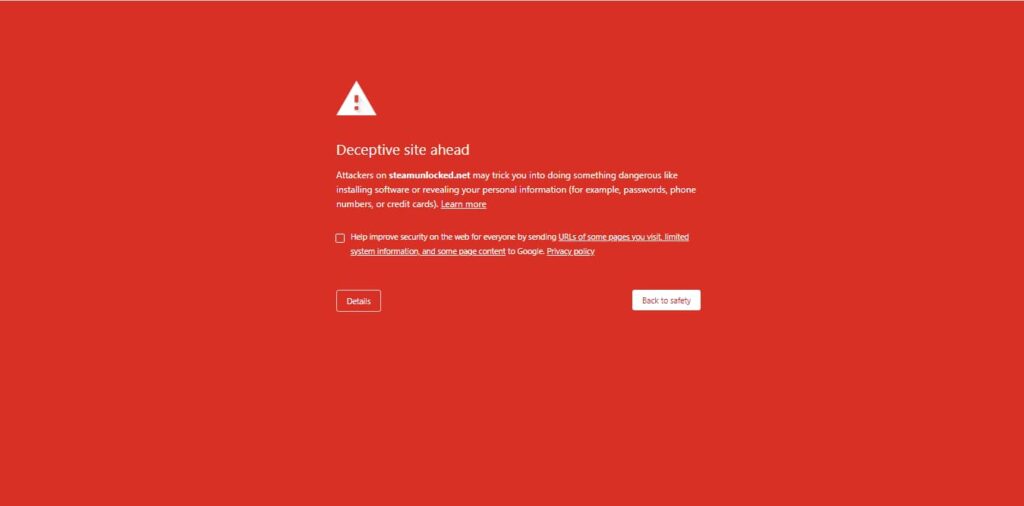
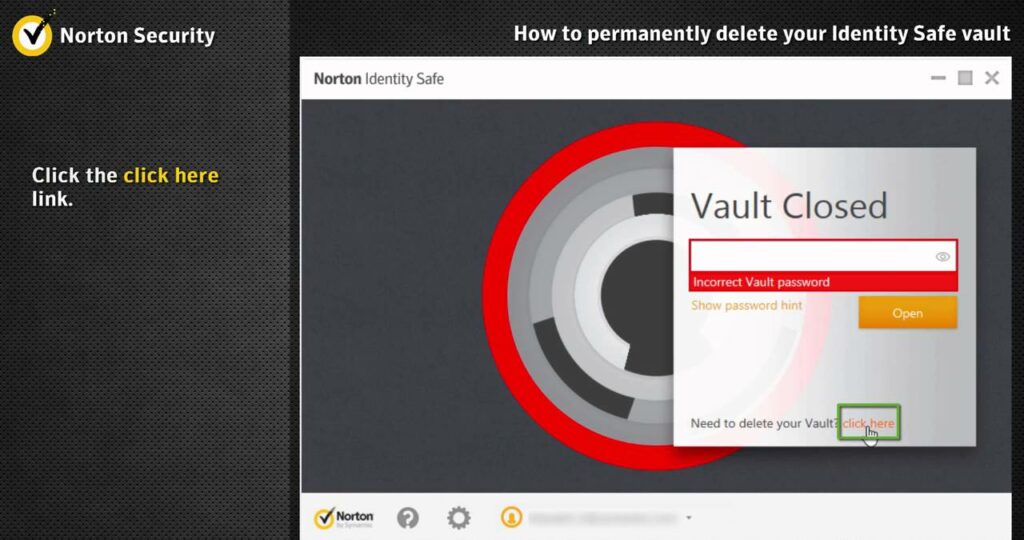
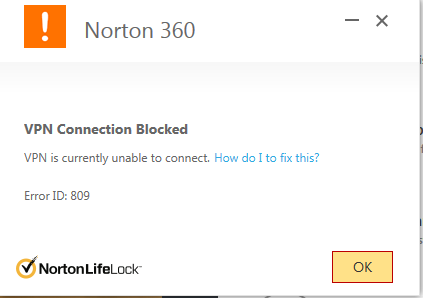
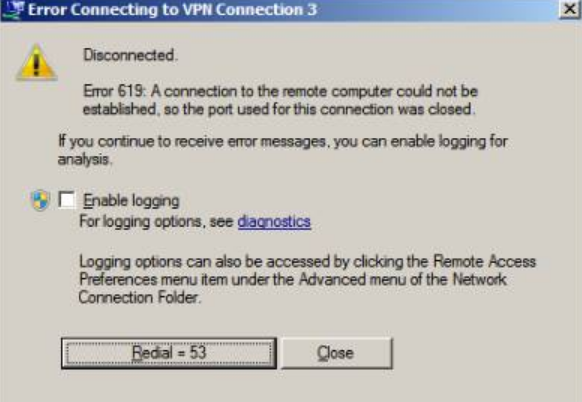
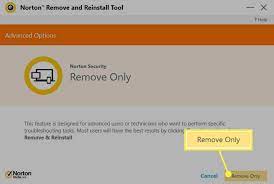
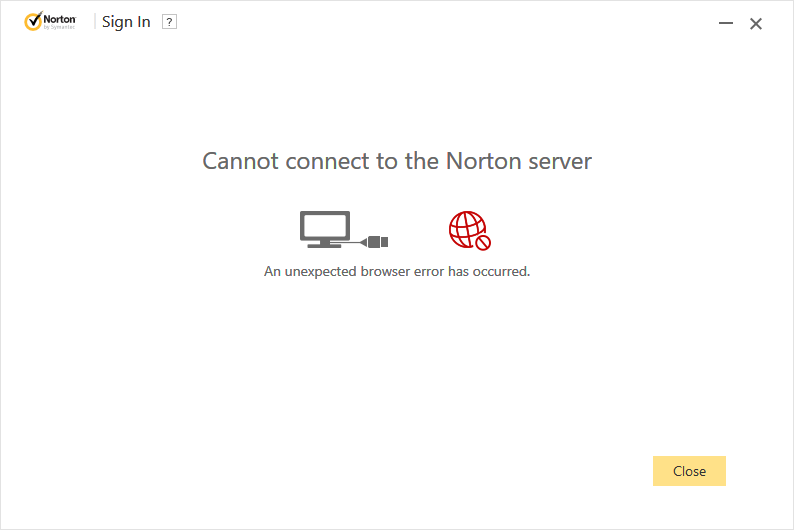
What to Do: Express Vpn On Apple Tv is not working?
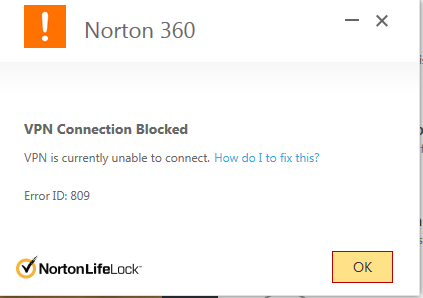
You can face issues with your setup often. It happens for many reasons, so it is your task to go and troubleshoot the controversy faced by your apple tv express VPN. Meanwhile, you must know that the media streamer is the prime power to create issues within the device. You can use expressvpn ben Shapiro for the express VPN security on Apple TV because this VPN is best for Apple TV. You can secure your security through the use of this VPN in comparison to other security VPNs.
Check out some ways to fix this issue.
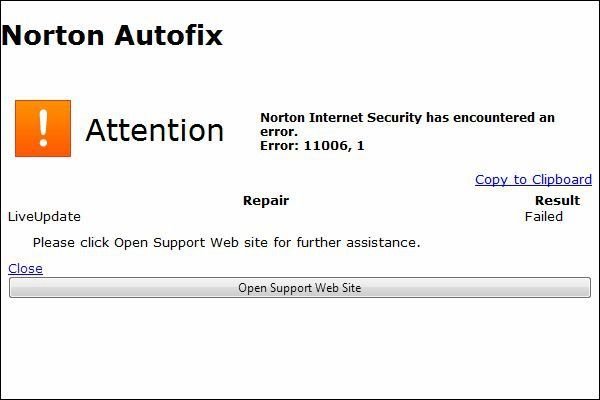
- Make sure your IP address is in an appropriate condition. If that is the case, follow to change the setting and register it again.
- Investigate the option you have chosen to install your Express VPN to your device and if the media streamer is creating an issue by blocking it for streaming. Kindly re-check the setup.
Wrapping Up
The article indicates that Express VPN supports your apple tv securely. You have this security shield to secure your network. However, the process is slightly different from other devices because the apple tv device doesn’t directly support your security. We should choose manual ways to attach your security key to our internet connection. Now make efforts to choose your plan and secure your network from malicious activities.
Frequently Asked Questions
Q.1 How to use express on Apple TV?
Go to the VPN website to download and install the app to make it trustworthy for your apple tv.
Q.2 How to get an express VPN on Apple tv?
Make sure to choose your plan from the company’s website to get an express Vpn on Apple TV.
Q.3 How to download express VPN on Apple tv?
You can download it from the official website or the Google Play Store.
Q.4 How to install express VPN on Apple tv?
As soon as you download the VPN, install it on the device by opening the downloaded file.